Special text characters are an integral part of typing. For the most part, however, they are not something that your normal, run-of-the-mill keyboard or laptop keypad is able to access easily. Luckily, for Windows 10 users, there is a shortcut that allows you to access all sorts of special characters.
Special text characters, like emojis, have become a part of the way that we communicate through text. While these expressive characters might not be something that businesses would include in formal content or some types of communications, even modern business correspondences call for the occasional smiley face.
Other special characters, like symbols of foreign currency or fractions, are even more commonly used in business but are still tricky to create using a traditional keyboard.
Windows 10 - Touch Keyboard
Before we lose those of you who are using Windows 10 on a desktop or laptop that doesn’t have a touch screen - Windows 10’s Touch Keyboard responds to mouse-clicks just as easily.
Note: Windows 10 users who don’t have the keyboard displayed on their screen can easily access it using the following three simple steps:
- Right click a blank spot on your taskbar.

- Click Show Touch keyboard button.
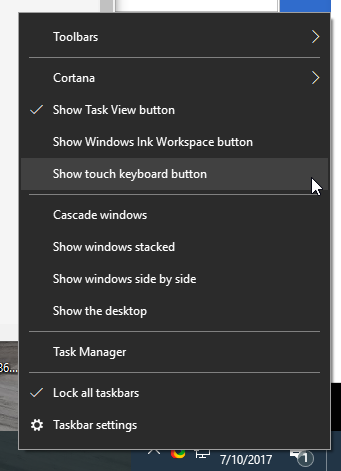
- Touch keyboard icon will appear to the left of the time clock on your taskbar.

Primary Touchpad Keyboard
Whenever you want to easily add a few special characters, simply click on the touch keyboard icon to pull up a keyboard that looks something like this: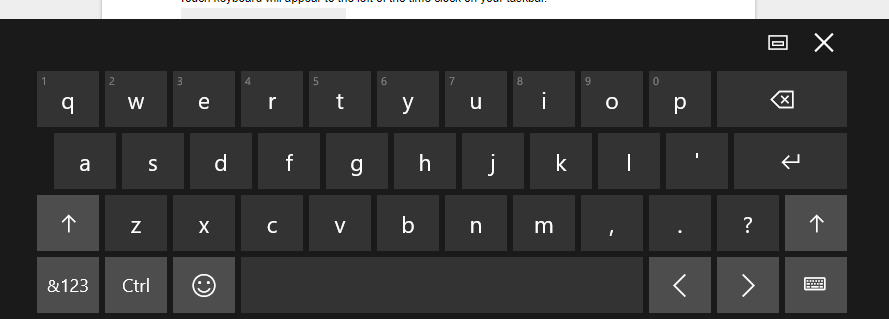
Related Characters
If you’re looking for a related character, clicking and holding will bring up a menu of similar letters. For example, some Spanish conversations might require the letter: ñ. To find this, simply click the letter ‘n’ and hold it, as depicted below: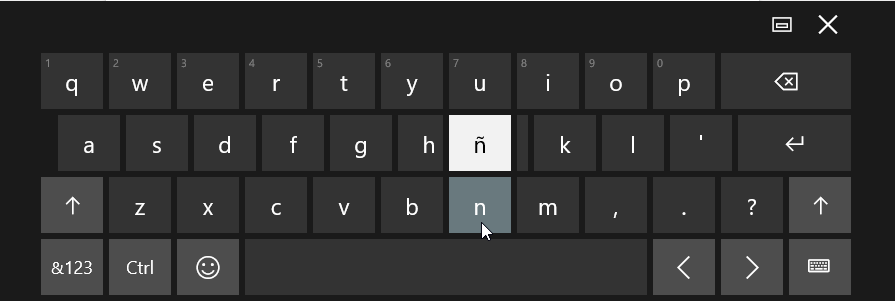
Punctuation and Numbers
For additional characters -and those related to them, click the button labeled &123 - highlighted below in red. 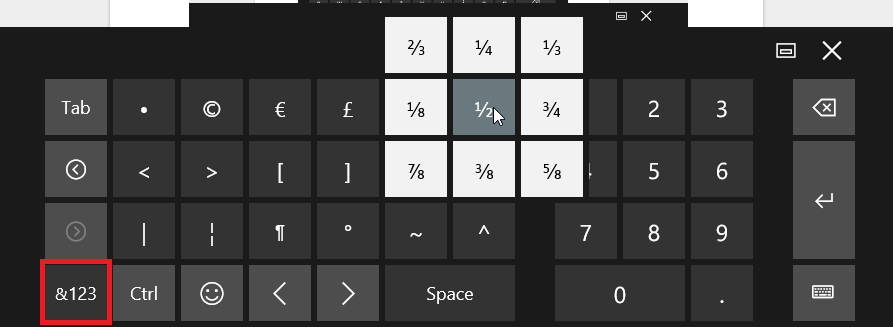
As with the primary keyboard, related characters are available by clicking and holding a key - as shown here with the ½ key.
Emojis
Clicking on the happy face emoji will transform your keyboard to a selection of faces and icons.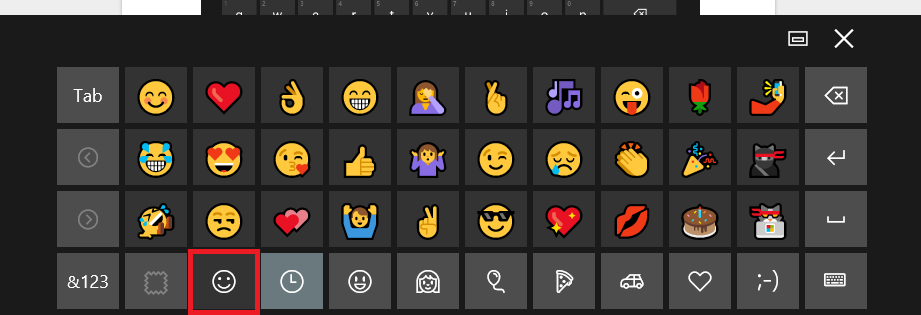
This is just one of the many awesome features that Windows 10 users can use to save them time and use technology to make life easier. Follow our blog for more great tips and tricks for Windows 10 and all things technology!



