Cloud computing has changed the way that businesses function, including some organizations that have foregone the on-premise server entirely in favor of it. Unfortunately, this approach can be problematic, as the data security and privacy issues associated with cloud-based resources might prove to be less than sustainable for your particular business.
Businesses that want to host their own IT infrastructure on-premises will need to be very careful about the technology they implement--particularly in regard to choosing hardware and network setup. This might seem intimidating, but it doesn’t have to be. Understanding the basics can help your business in the long run when implementing new hardware solutions. Here are a few pointers.
Get a Server Rack
If you’ve never had on-premise hardware, then you probably haven’t thought about what investing in this hardware means, including how long it will stay effective and where you will store it. You can kill two birds with one stone by purchasing a server rack. While it might seem like overkill, having a centralized location for your server units will keep you from suffering from a disorganized mass of wires and components that will need the attention of professionals to unhook properly. A rack can make your server infrastructure much easier to manage, but only if you get the one that suits your interests. Server racks are measured in rack units, or RU, and come in full-height (42U) or half-height (24U). The option for wall-mounted cabinets exists as well.
Whatever you choose, hosting your own hardware will mean that you need a place to store it. Servers are rather hot and loud, so they can range from being a distraction to being dangerous for your business continuity, when not properly managed. Isolating your company’s servers in a room designed for them provides a central infrastructure that can easily be maintained and managed. This brings us to our next point… cooling.
Cooling Your Infrastructure
When thinking about your infrastructure’s hardware, cooling is absolutely critical, and it should be a defining factor when thinking about moving your hardware to a new room. Your server room should, in theory, be climate-controlled with air conditioning and proper ventilation. If you’re using a proper data backup and disaster recovery solution, however, you’ll have a little more leeway in terms of climate control, particularly in regard to the heat given off by these units. If exposed to too much heat, server units will result in hardware failure and downtime.
Some organizations have HVAC systems that stop running when people leave for the day, but this is the last time you want your server units to be exposed to too much heat. Therefore, any server room with air conditioning or refrigeration will need to be set up independently of your organization’s HVAC system.
A Mess of Wires
Adding more hardware to your infrastructure will only make it more complicated, and when there are more machines on an infrastructure, there will be wires and cables that need to be managed. If you’re not careful about how you manage your servers, it might look something like the one on the left.
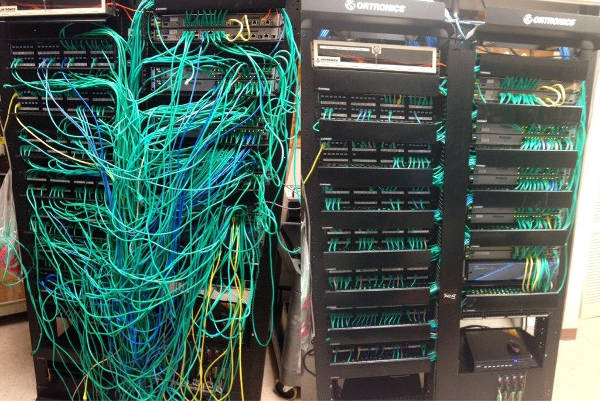
A complete renovation is somewhat necessary in order to recover from this situation. The one on the right looks fine, but only because a technician invested a lot of time and effort in making it organized. Labeling everything on the server rack is essential, as moving even a few cables could be enough to harm the network’s performance, and documenting what each unit is for will expedite maintenance on the technician’s end. A label printer with the hardware will make it so that you can label equipment based on names or IP addresses.
Hardware should only be handled by professional IT technicians, so why not invest in your business’ future with Voyage Technology? We can maintain and manage your hardware, whether it’s hosted on-premises or in the cloud. To learn more, reach out to us at 800.618.9844.



