Your smartphone is, without a doubt, a valuable business asset. It keeps you connected to your business at all times, even when you’re home; but is this a good thing? Have you ever considered what your significant other might feel if you answer your phone while out to dinner? Thanks to the indisputable power of social science research, it’s been proven that smartphones are bad for our personal relationships. Gasp!
Your smartphone is, without a doubt, a valuable business asset. It keeps you connected to your business at all times, even when you’re home; but is this a good thing? Have you ever considered what your significant other might feel if you answer your phone while out to dinner? Thanks to the indisputable power of social science research, it’s been proven that smartphones are bad for our personal relationships. Gasp!
This revelation, albeit somewhat obvious, was the result of a test led by Virginia Tech’s Shalini Misra. 100 pairs of strangers were set up to have 10-minute conversations in the Washington D.C. area. Half of the pairs were told to make small talk, while the other half discussed more personal, feeling-oriented topics. During the duration of the test, the research team recorded when, and how often, participants took out their mobile devices.
Following the survey, the participants were asked to complete a survey commenting on the quality of the conversation experienced. The results show that people feel smartphones reduce the quality of conversation, which in turn produces weakened relationships. Here are some of the observations that were made:
- Pairs who frequently used their mobile devices during conversation had a decreased sense of “interconnectedness,” which was determined by the survey with answers like “I felt close to my conversation partner.”
- Even the simple act of placing the device on the table worked against the test participants.
- Feelings of “empathetic concern,” which were measured by whether or not the conversationalists really understood the feelings of each other, also decreased.
It might seem inconsequential, but even the sight of a mobile device can make a situation feel less social. This can be detrimental to building new relationships, and maintaining previously-existing ones. If you think your smartphone is hampering your ability to be social, it might be time to examine your phone etiquette.
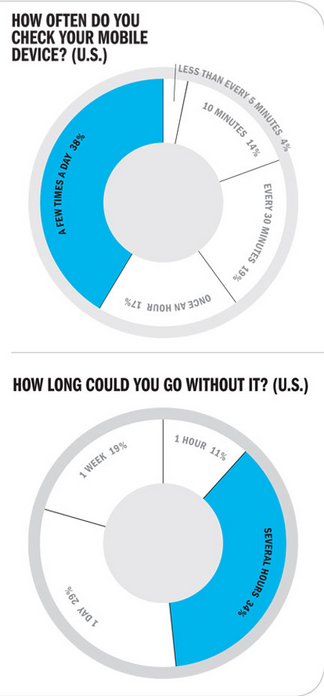
Challenge: Attempt to Go a Single Day Without Your Phone
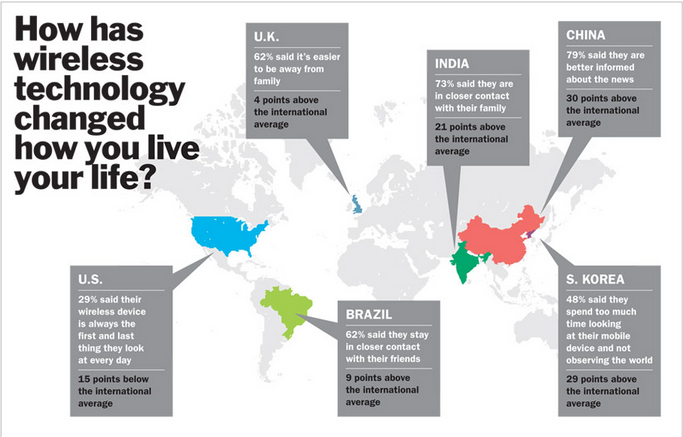
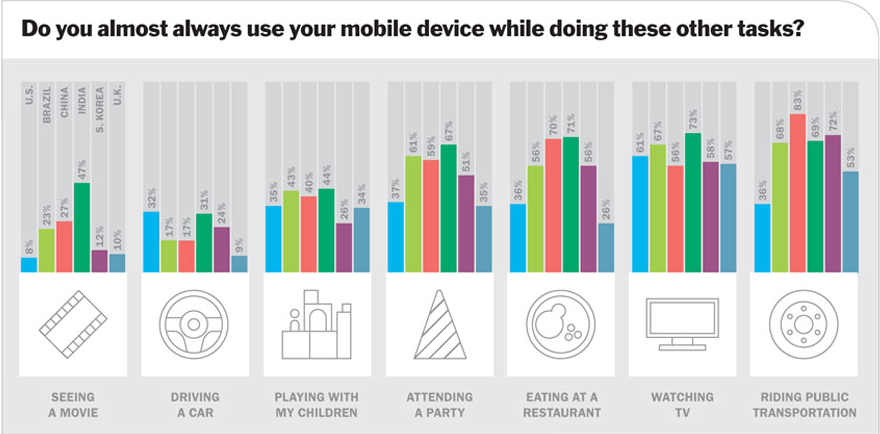
A 2012 study from Time magazine asked nearly 5,000 smartphone users to judge how reliant they were on their smartphones. The results revealed that society certainly does have a problem with smartphone addiction.
Take a Smartphone Break
Whether or not you’re using your smartphone for work or for sheer entertainment, you need to take a break from your smartphone once in a while. Unfortunately, the business owner might feel reluctant to separate from their mobile device. The important thing to remember is that a break from technology now and again is beneficial to your overall health and mental state. According to Scientific American, a certain amount of downtime is required in order to replenish productive, creative thought capabilities.
Instead of relying on your smartphone all of the time, it might not be a bad idea to let go and see how much you can get done without it. Andrew Smart’s book titled Autopilot: The Art and Science of Doing Nothing details how it can be beneficial to do this. According to Smart, this can lead to a better understanding of what your unconscious self wants, and can lead to you using that knowledge to your advantage.
Do you think you can keep the productivity up without being tethered to your device at all times? What are some of your tips for dealing with smartphone addiction? Let us know in the comments.