 There’s an intrusive malware on the Internet that locks a user out of their PC and directs them to a fake IT support phone number. In addition to being inconvenient, it can lead to the theft of sensitive information. If this happens to you, whatever you do, don’t call the fake phone number.
There’s an intrusive malware on the Internet that locks a user out of their PC and directs them to a fake IT support phone number. In addition to being inconvenient, it can lead to the theft of sensitive information. If this happens to you, whatever you do, don’t call the fake phone number.
This attack is a classic phishing scam tactic; scare a user into contacting the hacker for the purpose of turning over their sensitive information. Typically, phishing scams involve spam emails and the information is transferred via an attachment, like a form. While this email tactic has tricked plenty of users, it’s not very effective because the scam is fairly easy to spot, and once the email is determined to be a phishing scam, it then gets deleted or ignored.
When activated, this particular malware is a virtually impossible to ignore. It will hit your PC without warning and even while you’re visiting a secure site (like Facebook or Google search). Once the malware is executed, the browser will display an image similar to the Windows blue screen of death. A fake technical support message will then be displayed, informing the user of the nature of the problem and directing them to call a bogus phone number.
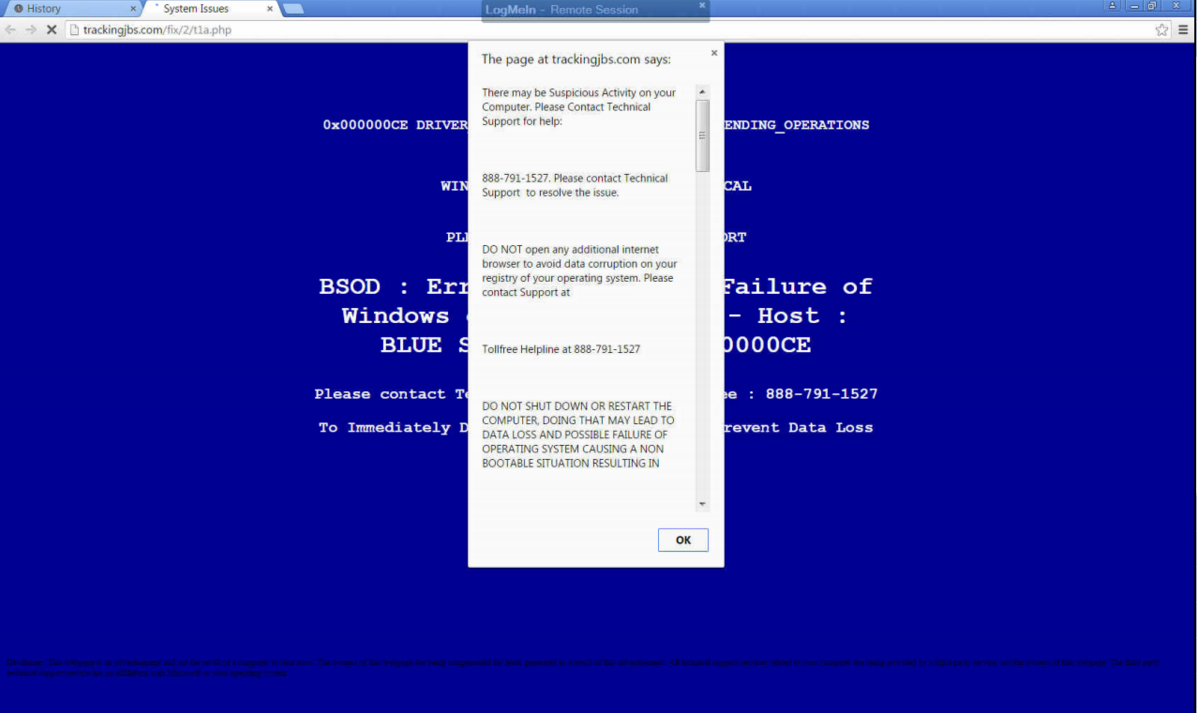
Unfortunately, this blue screen can’t be closed out and easily ignored. The malware will completely freeze up your browser, meaning that the only way to get rid of this annoyance is to either manually close the browser via task manager (Ctrl + Alt + Delete), or reboot the computer entirely.
This type of tactic is called social engineering, and modern hackers utilize these tactics to assist them in getting past security by poking at weaknesses in end-users. By getting an emotional response, whether it be the frustration of malware or your empathy by say, pretending to be a friend of yours on social media, the hacker is much more likely to find their way into your computer.
Having to take such extreme measures is sure to put a damper on any project that you’re currently working on, cause downtime, and may even delete unsaved data. That’s not all; just because you’ve rebooted your system, doesn’t mean the malware is gone. Unless the malicious file is located and properly deleted, it will remain on the hard drive and pop up at another random time.
To reiterate; DON’T CALL THE PROVIDED PHONE NUMBER. The blog Delete Malware explains the risk: “If you call [the number] they won't actually remove adware from your computer. They will hijack your computer and steal all of your bank information and passwords. They are crooks, don't call them!”
Instead, call the real IT professionals at 800.618.9844. By calling the fake phone number, you’re only opening yourself up to being taken deeper by this scam. One thing that hackers like these are counting on is you or your staff not having a solid understanding of who’s responsible for maintaining your company’s IT. It’s their hope that you’ll experience an error, panic, and call the provided number for “help.”
Actually, hackers posing as IT professionals is a fairly common scam. They like to pretend to be IT support because they know that users will trust their sensitive data to IT personnel (these jerks are giving IT professionals the world over a bad name). Therefore, it’s important to familiarize your staff with exactly who is overseeing their IT, and how to contact them, and only them, if there’s ever an issue.
By monitoring your network for risks, comprehensive IT support from Voyage Technology can protect your business from scams such as this. We can remotely find and eliminate threats, as well as equip your business with powerful security tools to keep destructive malware out of your system. Call the real IT pros at 800.618.9844 to learn more.


