 When it comes to technology, upgrading is part of the package. Despite this being a well-established fact, some business owners will delay upgrading for as long as possible, while others will upgrade as soon as the latest product is released. What’s behind a company’s motivation to upgrade or not? We can better understand this by looking at a study on why businesses upgrade their operating systems.
When it comes to technology, upgrading is part of the package. Despite this being a well-established fact, some business owners will delay upgrading for as long as possible, while others will upgrade as soon as the latest product is released. What’s behind a company’s motivation to upgrade or not? We can better understand this by looking at a study on why businesses upgrade their operating systems.
According to a recent study by Spiceworks, companies have different motivations for upgrading their workstation’s operating systems.
- 69 percent will only upgrade out of necessity, or “as needed.”
- 42 percent upgrade out of wanting to take full advantage of the latest apps supported by a new OS.
- 38 percent will only upgrade because their newly purchased hardware comes pre-installed with the latest operating system.
For additional reasons on why businesses will upgrade to a newer operating system, check out this chart from Spiceworks:
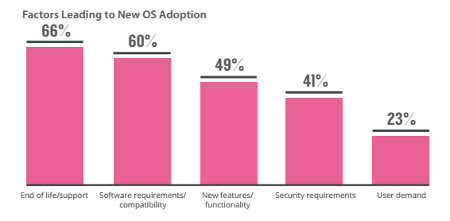
Here at Voyage Technology, we weren’t surprised when we saw that one of the top reasons for businesses to upgrade their OS was end-of-life events, coming in at 66 percent. We’ve seen this scenario play out recently with Microsoft ending support for both Windows XP and Windows 8. Now, for businesses that choose not to upgrade, despite being faced with an ultimatum by Microsoft to do so “or else,” we have to really wonder what their motivation is. Essentially, by not upgrading, they’re putting their company’s valuable data at risk.
One thing’s for sure: upgrading your operating systems isn’t something that should be taken lightly. For businesses dependent upon legacy software, they’re going to want to first test their mission-critical software on an isolated machine, before deploying it across their entire IT infrastructure. Failure to do so can result in some unwelcome surprises, like compatibility issues experienced in the middle of the workday, causing downtime and loss of productivity. Therefore, we recommend consulting with an IT professional before upgrading your company’s operating system--no matter what your reason may be for upgrading. This way, you’ll be able to take full advantage of every benefit that a new OS can afford your business.
Taking a look at upgrading a company’s operating system is an especially relevant topic to consider, thanks to the recent release of Windows 10. A business with multiple workstations and server units will want to put more thought into upgrading to a new OS like Windows 10 than the average consumer would. In the vast majority of cases, the benefits of upgrading to the latest technology far outweigh the risk, and thus, it’s well worth the investment. To get answers to all of your technology upgrading questions, give Voyage Technology a call at 800.618.9844.


